Loose Lips Sink Ships
Is There A Way To Stop Institutional Leaks?
Based on research by Prashant Kale, Kannan Srikanth, Anand Nandkumar, and Deepa Mani
Is There A Way To Stop Institutional Leaks?
- Specific workflow patterns can help offshore R&D centers keep a tighter grip on intellectual property.
- Spreading information widely within the company while limiting the depth of any one person’s knowledge makes leaks less damaging.
- Even inherently risky projects can be well secured with these techniques.
Offshoring has its tradeoffs. With their lower labor costs and growing talent pool, India and China entice many multinational corporations to launch research and development (R&D) centers. But both countries have weak patent enforcement regimes, which can expose companies to the pilfering of intellectual property. Highly mobile offshore employees and all-but-unenforceable non-compete agreements add to the risk. If today's employee heads to a rival company tomorrow, secrets are likely to leak.
For the parent company, the biggest worry is the leak of widely applicable new technology. When innovation is the product of a company's overall body of knowledge, a single leak can erode a firm’s entire competitive position. The stakes rise further when a process or product is fully documented, making it easier to create a competing product from scratch.
Luckily, managers of offshore R&D centers can limit their risk, according to Rice Business professor Prashant Kale and three colleagues. In a 2015 study of offshore R&D centers in India, the team identified six organizational mechanisms to help keep corporate secrets safe.
All six were based on two principles: 1) Minimize the leakable information; and 2) ensure that anything that does reach your competitors is of little use to them.
To measure how common these mechanisms were, Kale’s team surveyed managers of 142 Indian R&D centers in the energy, pharmaceuticals, semiconductor, IT hardware and software sectors.
The first practice the scholars identified: Break down the R&D division's knowledge base into interlocking fragments, like parts of a jigsaw puzzle. Distribute a large share of the puzzle pieces to workers at the home location.
Second, stress interdependence. Projects executed at headquarters should depend heavily on activities at offshore locations, and vice versa. Third, managers should tie R&D knowledge to specific assets within the company. By doing so, they help guarantee that a rival company without these assets won’t be able wring much value out of leaked knowledge.
By the same token, the fourth practice is to give headquarters control over project selection, design, implementation and/or operations. Fifth, relay key, substantive information from headquarters to the offshore location – and do it often. Using this mechanism, executives who spot a good idea can blend it with complementary knowledge from other locations. The mix makes an idea both more valuable and harder to copy.
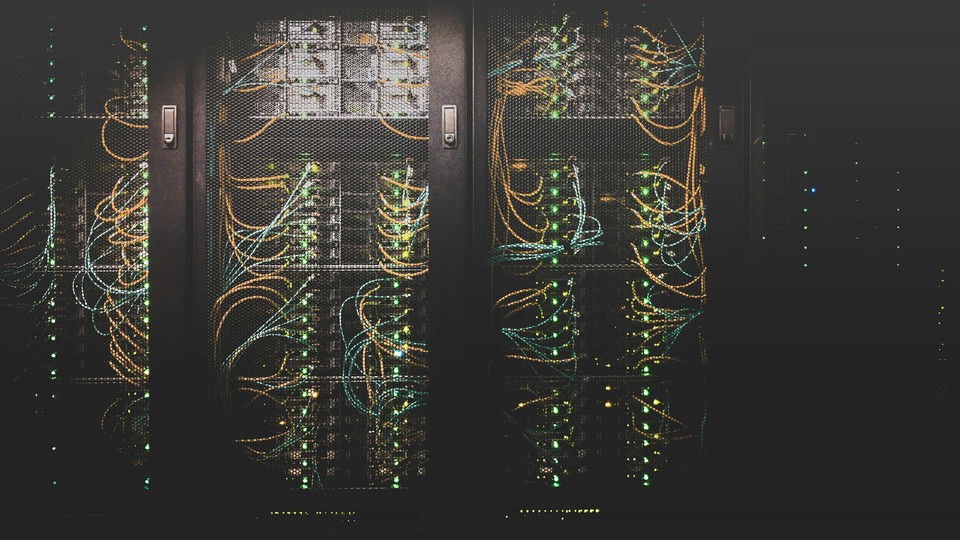
Finally, set up internal controls so no single person has all the information a rival needs to copy an innovation. This could mean storing critical data in more than one database, controlling access to that data, placing protected servers elsewhere or even assigning employee teams to separate, restricted-access work spaces.
Each of these six measures, the researchers found, boosts worker dependence on the system as a whole and arranges a company's institutional knowledge into more complex patterns. Competitors who get hold of leaked information won’t get much out of it if they can’t understand the components of a process and how they all fit together.
None of the respondents had adopted all six safeguards, Kale and his team noticed. Nevertheless, most companies who used one or more of these strategies reported confidence that their intellectual property was secure. They could have been mistaken, of course. But the researchers chose to use high confidence levels as a proxy for successful intellectual property security, explaining that objective data “on the extent of actual leakage … are notoriously hard to obtain.”
Interestingly, the managers’ confidence also changed the way their firms did business. Emboldened by their sense of security, Kale found, many firms in the study took on riskier projects and, in some cases, chose to hire more personnel.
Risk, the homily says, goes hand in hand with opportunity. For offshore enterprises that manage that risk intelligently, the opportunities can benefit both parent firm and local hires abroad.
Prashant Kale is associate professor of strategic management at Jones Graduate School of Business at Rice University.
To learn more, please see: Srikanth, K., Nandkumar, A., Kale, P., & Mani, D. (2015). The role of organizational mechanisms in preventing leakage of unpatented knowledge. Academy of Management Proceedings, 2015(1), 1206.
Never Miss A Story